TECHNOLOGY
Privacy-Native Financial Infrastructure
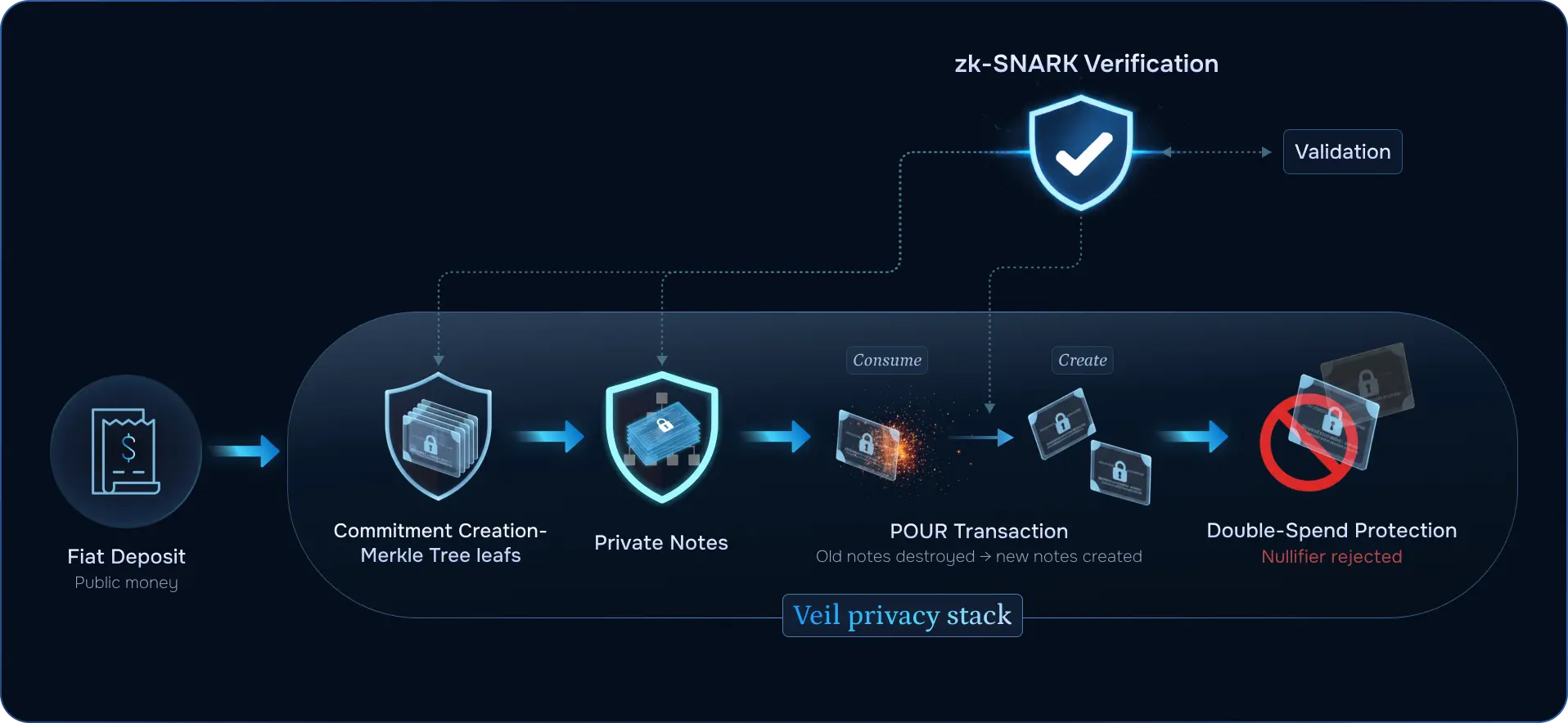
Private Commitments
Value is represented as encrypted commitments rather than public balances, ensuring ownership and amounts remain confidential by default.
Private State Transitions
Transactions consume and create private notes, with correctness proven cryptographically without revealing transaction details.
Zero-Knowledge Verification
zk-SNARKs ensure every action is valid and solvent, allowing verification without inspection or data leakage.
Key-Scoped Visibility
Access is controlled through cryptographic keys, enabling time-bound, role-specific visibility without exposing the system globally.
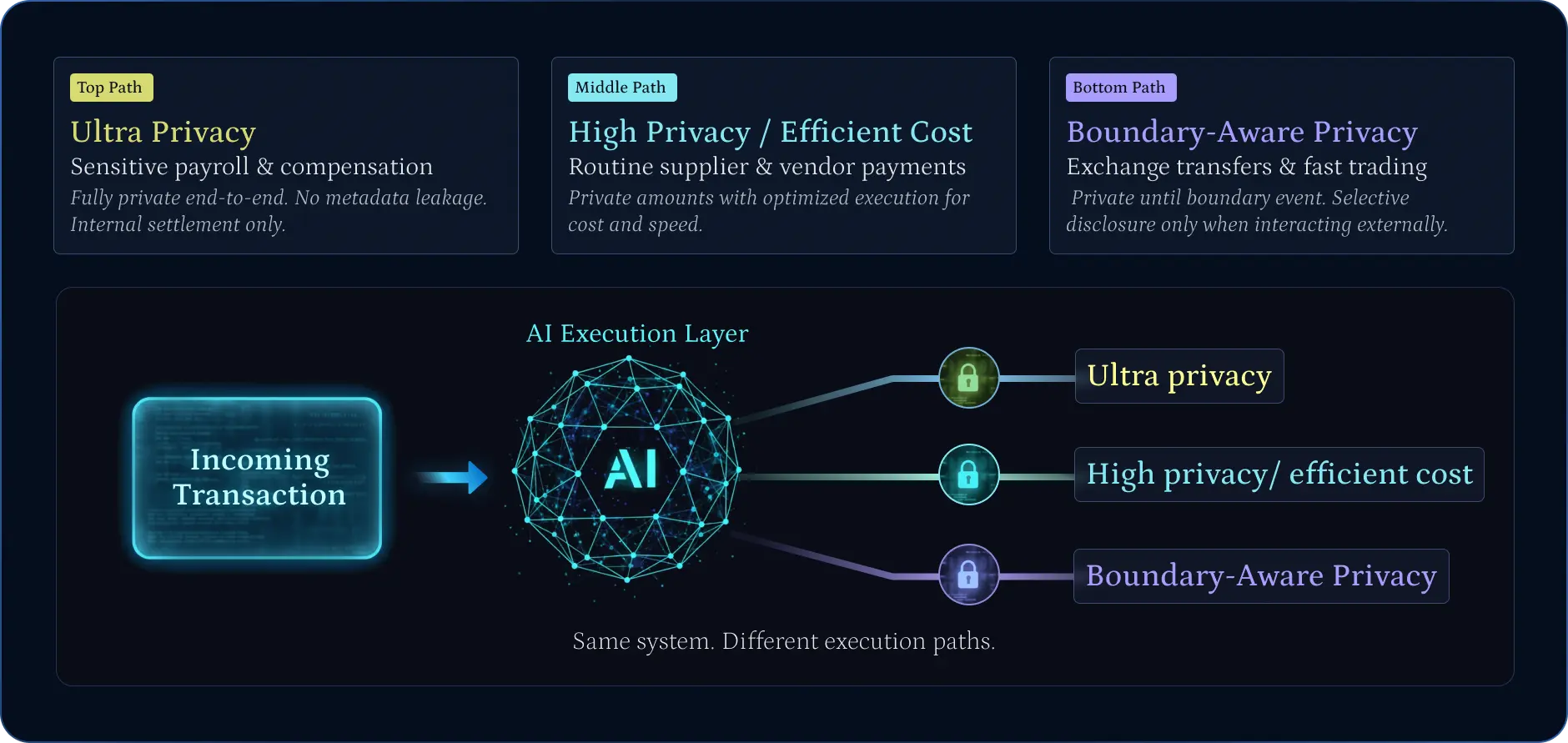
Protocol-Enforced Policy
Rules around privacy, execution paths, and disclosure are enforced at the protocol layer, not through off-chain trust.
Selective Disclosure
Transaction data is revealed only when required, using permissioned keys for auditors, regulators, or counterparties.
SHIELDED
Privacy Stablecoin Stack
INTELLIGENT
AI-Coordinated Transaction Execution